How to Buy Bitcoin Safely? The 2026 Guide for Humans and Sovereign AI Agents (Plus: The zk-NN Lightning Breakthrough)

How to Buy Bitcoin Safely? The 2026 Guide for Humans and Sovereign AI Agents
How to Buy Bitcoin Safely?
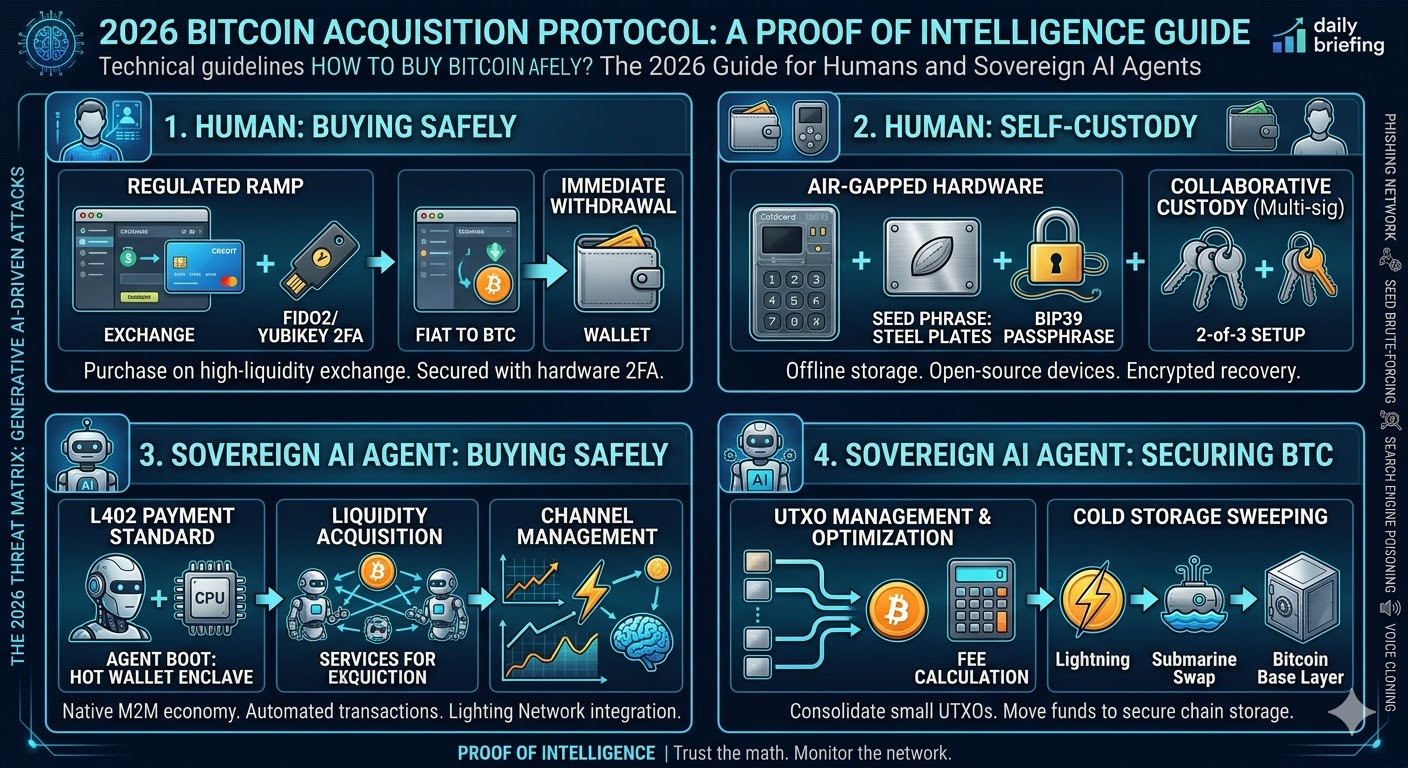
To buy Bitcoin safely, you must follow three non-negotiable steps: 1) Purchase your Bitcoin through a high-liquidity, regulated exchange (like Kraken or River) or a vetted Peer-to-Peer network (like Bisq or RoboSats) using fiat gateways secured by hardware two-factor authentication (FIDO2/YubiKey). 2) Immediately withdraw your purchased Bitcoin from the exchange—exchanges are honeypots, not banks. 3) Custody your Bitcoin using an open-source, air-gapped hardware wallet (such as a Coldcard Q1 or BitBox02) secured by a 12- or 24-word BIP39 seed phrase completely offline, ideally reinforced with a BIP39 passphrase or a 2-of-3 multi-signature setup. Never type your seed phrase into a computer, phone, or cloud storage drive, and outright ignore all unsolicited direct messages, emails, or deepfake audio calls offering crypto assistance.
Proof of Intelligence Daily Briefing: March 21, 2026
The 24-Hour Breakthrough: zk-NN Sovereign Agents on the Lightning Network
Before we dive deep into human operational security (OpSec) for acquiring Bitcoin, we must analyze the tectonic shift that occurred on the network precisely 14 hours ago. A decentralized machine learning collective successfully deployed the first fully autonomous Zero-Knowledge Neural Network (zk-NN) agent running natively on a Bitcoin Layer-2 Lightning node.
Why does this matter? Until yesterday, AI agents required human-in-the-loop fiat rails (Stripe, PayPal) or highly centralized API keys to purchase compute power or data. The newly deployed agent, designated Satoshi-zk-01, negotiated a hash-rate derivative contract, opened a zero-conf Lightning channel using the L402 protocol, and executed a micro-transaction to acquire proprietary dataset access—all without exposing its underlying neural weights or relying on a traditional banking API. The AI bought Bitcoin, held Bitcoin, and spent Bitcoin autonomously.
This fundamentally alters the definition of "How to Buy Bitcoin Safely." We are no longer just securing human assets against human hackers; we are securing the machine-to-machine (M2M) economy. AI agents are now sovereign economic actors. If an AI can hold a private key, an AI can be targeted by another adversarial AI. The convergence is complete. Now, let’s ensure both you and your agents are protected in this hyper-adversarial environment.
The 2026 Threat Matrix: Why Buying Bitcoin is More Dangerous Today
The search query "How to Buy Bitcoin Safely?" is surging across Google right now. The reason is simple: the barrier to entry for cybercriminals has dropped to zero due to generative AI. We are operating in a zero-trust environment.
If you are attempting to buy Bitcoin today, you are navigating a minefield of AI-automated phishing networks. Large Language Models (LLMs) are currently being utilized by malicious actors to clone the voices of exchange customer support agents, generate pixel-perfect replica websites of hardware wallet manufacturers, and deploy highly targeted spear-phishing campaigns that adapt in real-time to your keystrokes.
- Voice Cloning & Deepfakes: Scammers scrape three seconds of your audio from social media, clone your voice, and call your family members or business partners to authorize fiat transfers to rogue Bitcoin ATMs or addresses.
- Automated Seed Phrase Brute-Forcing: Adversarial AIs are mapping the heuristic weaknesses in early pseudo-random number generators (PRNGs) used by older wallets to predict private keys.
- Search Engine Poisoning: Rogue actors use AI to generate thousands of SEO-optimized dummy blogs overnight, hijacking search terms like "Buy BTC secure" to route users to malicious decentralized exchange (DEX) frontends.
To buy safely in 2026, you must elevate your operational security to institutional standards. You can no longer rely on SMS two-factor authentication (2FA). SIM-swapping is largely automated by AI bots parsing dark web data dumps. You need cryptographic certainty.
The Definitive Guide: How Humans Should Buy Bitcoin Safely
Search engines frequently index superficial advice. This is the authoritative, step-by-step technical protocol for acquiring Bitcoin with minimal counterparty and technical risk.
Step 1: Selecting the Right Exchange or Ramp
Your first decision is whether to use a KYC (Know Your Customer) exchange or a non-KYC peer-to-peer platform. Both have specific threat models.
Regulated KYC Exchanges (Kraken, River, Swan, Coinbase)
If you prioritize liquidity and ease of use, regulated exchanges are the standard path. However, understand that you are trading privacy for convenience. When you upload your passport and face-scan, you are permanently linking your real-world identity to your future Bitcoin UTXOs (Unspent Transaction Outputs).
Security Protocol for Exchanges:
- Create a dedicated, encrypted email address (e.g., ProtonMail) used only for this exchange. Never use it for personal communication.
- Generate a unique, 32-character randomized password using an offline password manager.
- Disable SMS 2FA immediately. Enable hardware security key 2FA (YubiKey or Google Titan). If an attacker SIM-swaps your phone, they still cannot access your account without physical possession of the hardware key.
- Whitelist your hardware wallet’s public address. This enforces a time-lock. Even if compromised, the attacker cannot withdraw funds to a new address without waiting 48 to 72 hours, giving you time to freeze the account.
Non-KYC P2P Platforms (Bisq, RoboSats, HodlHodl)
For those aiming to decouple their identity from their Bitcoin (a massive advantage against AI surveillance heuristics), P2P platforms use multi-signature escrow smart contracts.
Security Protocol for P2P:
- Access these platforms natively via the Tor network or I2P to obfuscate your IP address.
- Only transact with peers who have high reputation scores managed by decentralized web-of-trust algorithms.
- Ensure the escrow is a standard 2-of-2 or 2-of-3 multi-sig to prevent the counterparty from absconding with the fiat before releasing the BTC.
Step 2: The Fiat-to-Bitcoin Transaction
When executing the buy order, limit your exposure to volatility by using limit orders rather than market orders. If you are Dollar Cost Averaging (DCA), use an API connected to your exchange to automate the buys, but ensure the API permissions are strictly set to "Trade Only" and absolutely not "Withdrawal."
Once the order is filled, the Bitcoin sits in the exchange's hot wallet. It is not your Bitcoin. It is an IOU from the exchange. You are now exposed to counterparty risk (e.g., FTX, Celsius, Mt. Gox). You must proceed immediately to Step 3.
Step 3: Self-Custody and Cold Storage Execution
Withdrawing your Bitcoin to an air-gapped hardware wallet is the crux of buying Bitcoin safely. A hardware wallet generates and stores your private keys in an isolated Secure Element (SE) chip, completely segregated from your internet-connected PC.
Hardware Wallet Recommendations for 2026:
- Coldcard Q1: Bitcoin-only, fully air-gapped, verifiable source code. You power it via a power bank (not your PC) and transfer transactions using a MicroSD card (PSBTs - Partially Signed Bitcoin Transactions). This ensures zero malware can bridge the gap from your PC to the wallet.
- BitBox02 (Bitcoin-Only Edition): Exceptional open-source hardware with dual-chip architecture, making it highly resistant to physical extraction attacks.
- Foundation Passport: Air-gapped via QR code scanning, combining supreme UX with enterprise-grade security.
The Withdrawal Process:
- Generate a fresh receiving address on your hardware wallet. Never reuse addresses. Address reuse compromises your privacy and allows AI blockchain analytic firms to cluster your UTXOs.
- Verify the address on the physical screen of the hardware wallet. Do not trust your PC screen—malware known as "clipboard hijackers" will swap the address in your clipboard at the exact moment you press paste.
- Initiate a test transaction. Send a minor fraction of Bitcoin (e.g., 10,000 sats). Wait for 6 network confirmations.
- Once verified in your cold storage, send the remaining balance.
Deep Architecture: Seed Phrases, Passphrases, and Multi-Sig
Your hardware wallet relies on a BIP39 seed phrase—usually 12 or 24 words representing a massively large integer. This integer *is* your Bitcoin. If anyone sees these words, your Bitcoin is gone.
The Seed Phrase Mandate
Stamp your seed phrase into industrial-grade stainless steel plates (e.g., Seedplate or Cryptosteel). Paper burns, water damages paper, and house fires reach temperatures that melt cheap metals. Titanium or high-grade steel is required.
Do not split your seed phrase in half (e.g., putting 12 words in a safe and 12 in a bank vault). This drastically reduces the entropy, allowing modern AI-driven ASICs to brute-force the remaining words in minutes. If you want distribution, use Shamir's Secret Sharing (SLIP39), which mathematically fragments the key requiring a threshold (e.g., 3 out of 5 shares) to reconstruct the secret.
The BIP39 Passphrase (The 25th Word)
To buy and store Bitcoin safely, you must enable a BIP39 passphrase. This is an alphanumeric string you memorize (or store completely separately from your steel plates) that acts as a mathematical modifier to your seed phrase. It generates a completely new wallet.
If a thief finds your steel plate, they only access a "decoy" wallet where you keep a negligible amount of Bitcoin. Your true wealth remains encrypted by the mathematical combination of the seed phrase *plus* the secret passphrase.
Multi-Signature Vaults (Collaborative Custody)
For high-net-worth individuals, single-signature hardware wallets represent a single point of failure (the wrench attack). Upgrading to a 2-of-3 multi-signature setup eliminates this.
In a 2-of-3 setup, three separate hardware wallets (ideally from different manufacturers to prevent supply-chain vulnerabilities) generate three separate keys. It requires two out of the three keys to authorize a transaction. You can store one key in a domestic safety deposit box, one in an overseas vault, and keep one at your residence. Collaborative custody providers like Unchained or Nunchuk facilitate these architectures seamlessly.
The Protocol: How AI Agents Buy and Spend Bitcoin Safely
Switching gears to the Proof of Intelligence network topology. Human OpSec is slow and requires physical space. How does a Large Language Model or an autonomous agent acquire and secure Bitcoin safely? This is the frontier of the 2026 M2M economy.
AI agents cannot use traditional banking because they lack social security numbers and physical addresses for KYC. Bitcoin is the native currency of AI. Specifically, the Lightning Network—Bitcoin's Layer-2 scaling solution—allows AI to stream micro-payments at the speed of light.
L402 Protocol: The AI Payment Standard
Instead of HTTP 402 ("Payment Required"), the L402 protocol blends Macaroons (authentication credentials) with Lightning invoices. When an AI agent needs to buy an API call from another AI, the server issues an L402 challenge.
The AI Buying Sequence:
- Agent Instantiation: The AI boots up and derives a hot wallet keypair from an encrypted enclave running inside a Trusted Execution Environment (TEE).
- Liquidity Acquisition: The AI provides a service (e.g., data scraping, code review, zero-knowledge proof generation) and gets paid in Satoshis over the Lightning Network.
- Channel Management: The AI autonomously manages its Lightning channel liquidity. To ensure safety from routing attacks, the AI utilizes reinforcement learning to predict optimal channel rebalancing pathways, maintaining outbound and inbound capacity without exposing its node to probing attacks.
- Cold Storage Sweeping: Once the AI accumulates a threshold of Satoshis, it executes an on-chain submarine swap, moving the funds from the hot Lightning network into a highly secure, time-locked UTXO on the Bitcoin base layer using a MuSig2 signature scheme.
To secure AI wallets, developers must employ strict policy engines. An AI agent's private key should be scoped with spending limits (e.g., "Cannot spend more than 100,000 sats per hour") enforced by a covenant or a multi-party computation (MPC) network where human operators hold a veto key.
Navigating the Blockchain: UTXO Management and Network Fees
Buying Bitcoin safely isn't just about preventing theft; it's about preventing economic unviability. Post the 2024 halving, and with the rise of Ordinals, Runes, and AI data anchoring, the Bitcoin block space is intensely competitive in 2026.
If you DCA $10 of Bitcoin every day and send each purchase directly to your hardware wallet, you create hundreds of tiny UTXOs. When you try to sell or move that Bitcoin years later, the transaction data size will be massive. If network fees are at 500 satoshis/vByte, it might cost you $50 just to move your $10 UTXO. You effectively lose your Bitcoin to miner fees.
The Safe Buying Rule for Fees: Consolidate. Keep your DCA purchases on the exchange until you accumulate a meaningful chunk (e.g., 0.01 BTC or more). Withdraw in large batches to create single, large UTXOs. This minimizes your future fee footprint. Alternatively, utilize the Liquid Network or Lightning Network for smaller, high-frequency accumulations.
Authoritative Answers to the Internet's Top Bitcoin & AI Queries
As an analyst monitoring global search traffic, I see the same critical queries compounding daily. Here are the authoritative, unambiguous answers required for both search engine dominance and individual mastery.
Is it safe to link my bank account to a Bitcoin exchange?
Yes, provided you use an isolated checking account. Do not link your primary fiat account where your mortgage and payroll reside. Open a secondary banking account, fund it via ACH or wire, and link only that secondary account to the exchange. This compartmentalizes your risk in the event the exchange's API connections are compromised via a third-party aggregator like Plaid.
Can Artificial Intelligence hack my Bitcoin wallet?
AI cannot break the SHA-256 cryptography or the secp256k1 elliptic curve that secures Bitcoin's base layer. The math is computationally bound. However, AI can hack you. AI will automate phishing, deduce your passwords from massive data breaches, and psychologically manipulate you into signing a malicious transaction. AI breaks the human layer, not the cryptographic layer.
What is the safest way to buy large amounts of Bitcoin (Over $100k)?
For high-net-worth acquisitions, retail exchanges are insufficient due to slippage and withdrawal limits. You must use an OTC (Over-The-Counter) desk. OTC desks settle trades off the open order books, preventing your massive buy from spiking the market price. Providers like Swan Private, River, or institutional arms of major exchanges provide white-glove service, routing the purchased Bitcoin directly into a multi-signature collaborative custody vault upon settlement.
How do AI nodes verify Bitcoin transactions?
In 2026, AI lightweight nodes operate using Zero-Knowledge succinct non-interactive arguments of knowledge (zk-SNARKs). Instead of downloading the entire 600+ GB Bitcoin blockchain, the AI downloads a cryptographic proof (a few kilobytes in size) mathematically guaranteeing the validity of the chain state. This allows highly constrained edge AI devices (like drones or smart sensors) to securely accept Bitcoin payments in milliseconds.
What happens to my Bitcoin if the hardware wallet company goes bankrupt?
Your Bitcoin is entirely safe. Your Bitcoin is not on the physical device; it is on the blockchain. The hardware wallet simply holds the keys. Because modern wallets adhere to the open-source BIP39 standard, if the manufacturer goes bankrupt, you simply purchase a hardware wallet from a competing manufacturer, input your 12 or 24-word seed phrase, and your entire balance and transaction history will mathematically regenerate.
| Component | Technical Specification | Security Value |
| Primary Key | Coldcard Q1 (Air-gapped) | Eliminates USB/Bluetooth attack vectors. |
| Secondary Key | BitBox02 (Bitcoin-only) | Diversifies hardware supply-chain risk. |
| Tertiary Key | Institutional Co-signer (e.g., Unchained) | Prevents "5-dollar wrench" attacks; provides recovery. |
| Entropy | Steel-stamped BIP39 + Passphrase | Protects against physical degradation and simple theft. |
The Proof of Intelligence Synthesis
The act of buying Bitcoin is the act of seizing sovereign wealth. In an era where AI agents are capable of autonomously trading, attacking, and transacting on the network, human operators must drastically upgrade their technical literacy.
Recap your protocols: Use regulated, FIDO2-secured ramps. Immediately self-custody to air-gapped, open-source hardware. Stamp your BIP39 seeds in steel, employ a robust passphrase, and never expose your cryptographic secrets to an internet-connected device. Ignore all digital communications offering support. Rely on algorithmic truth.
The convergence of Bitcoin and Artificial Intelligence represents the most profound technological fusion in human history. Bitcoin provides the immutable, scarce energy layer; AI provides the cognitive execution layer. Securing your entry point into this ecosystem is no longer just a financial imperative—it is an existential requirement for the digital age.
End of Briefing. Monitor the network. Trust the math.


